Advanced Threat Protection
Email-borne malware against organizations continues to be a popular tool for malicious attackers. Chatham, per best security practice, already has a solution in-place with Microsoft Office 365 to help protect you against most known malicious email attachments and website links. However, attackers continue to evolve their threats and create new attachments and websites that contain malicious content but are not yet known to the security industry. These attacks are commonly referred to as “zero-day exploits” as signatures to detect these threats are not yet developed by the security industry.
Chatham University has chosen to make an additional investment in our organizations security defenses by implementing a solution called Microsoft Advanced Threat Protection (or ATP for short) to protect us against these “zero-day exploits”. ATP is designed to catch malicious attachments and/or links to malicious websites that may appear in emails you receive. In advance of our deployment of ATP, we want to make sure you are aware of any potential changes to your email.
ATP is made up of two different security features which we explain in more detail along with potential changes you may notice in the following descriptions:
Safe Attachments
The safe attachments feature of ATP starts by checking the attachment and comparing the file to known file signatures. If the file is known good, the attachment is passed through the system immediately. If the signature for the file is known bad, the attachment is quarantined and you will be notified that the attachment was blocked.
The next scenario is the core purpose of the safe attachments solution and will slightly impact the way you receive emails. If the attachment does not have a known signature, the attachment is temporarily removed from the email and replaced with a “preview” link to the document. The rest of the email is delivered to you immediately. In the meantime, the attachment is sent to Microsoft where it is tested for malicious intent. Once the scan is complete, known good attachments will be reattached to the email while known bad files will be quarantined.
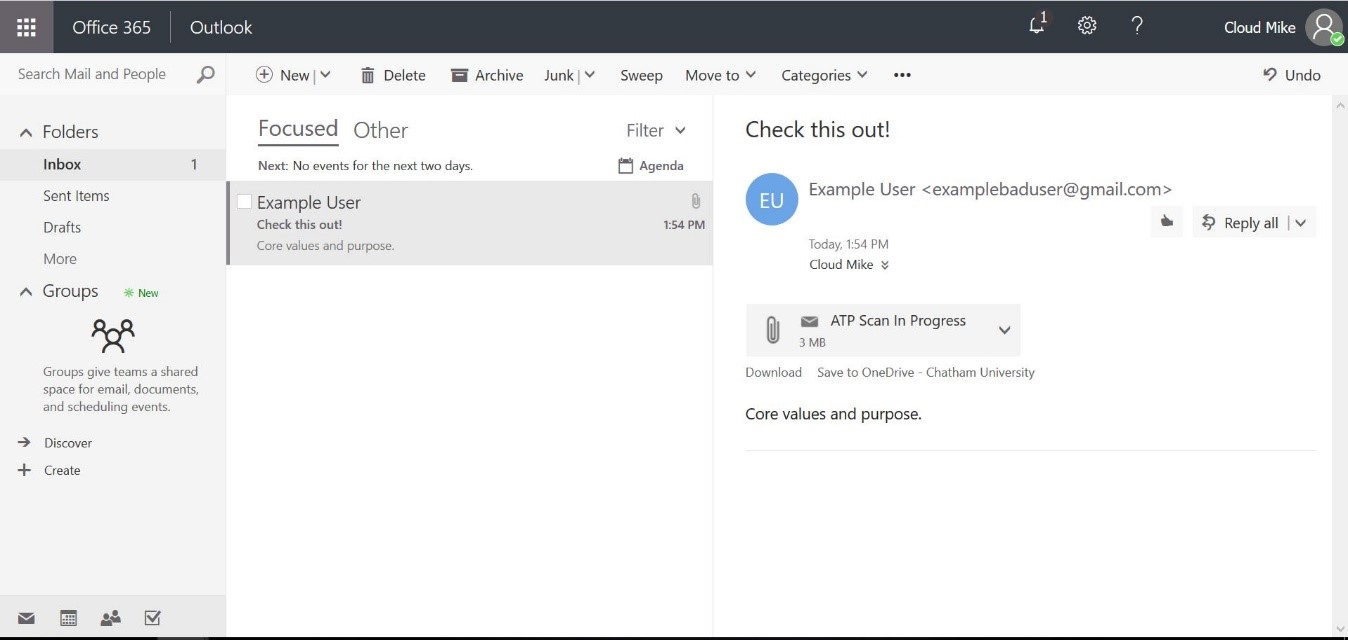
While attachments are being scanned, you will receive an email that looks like the following screenshot:
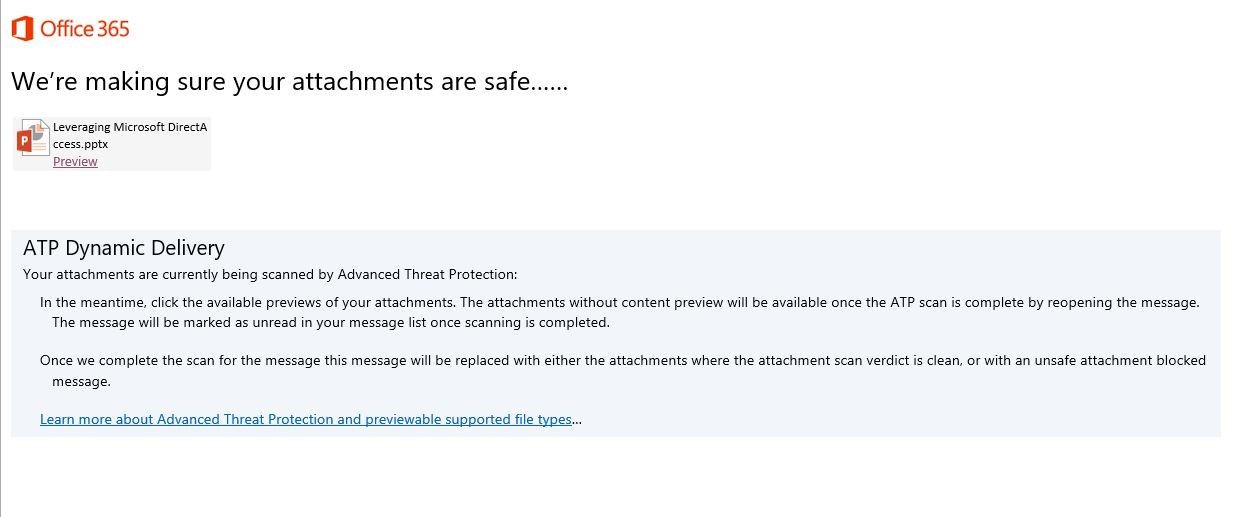
Opening the attachment named “ATP Scan in Progress” will display a message similar to the following:
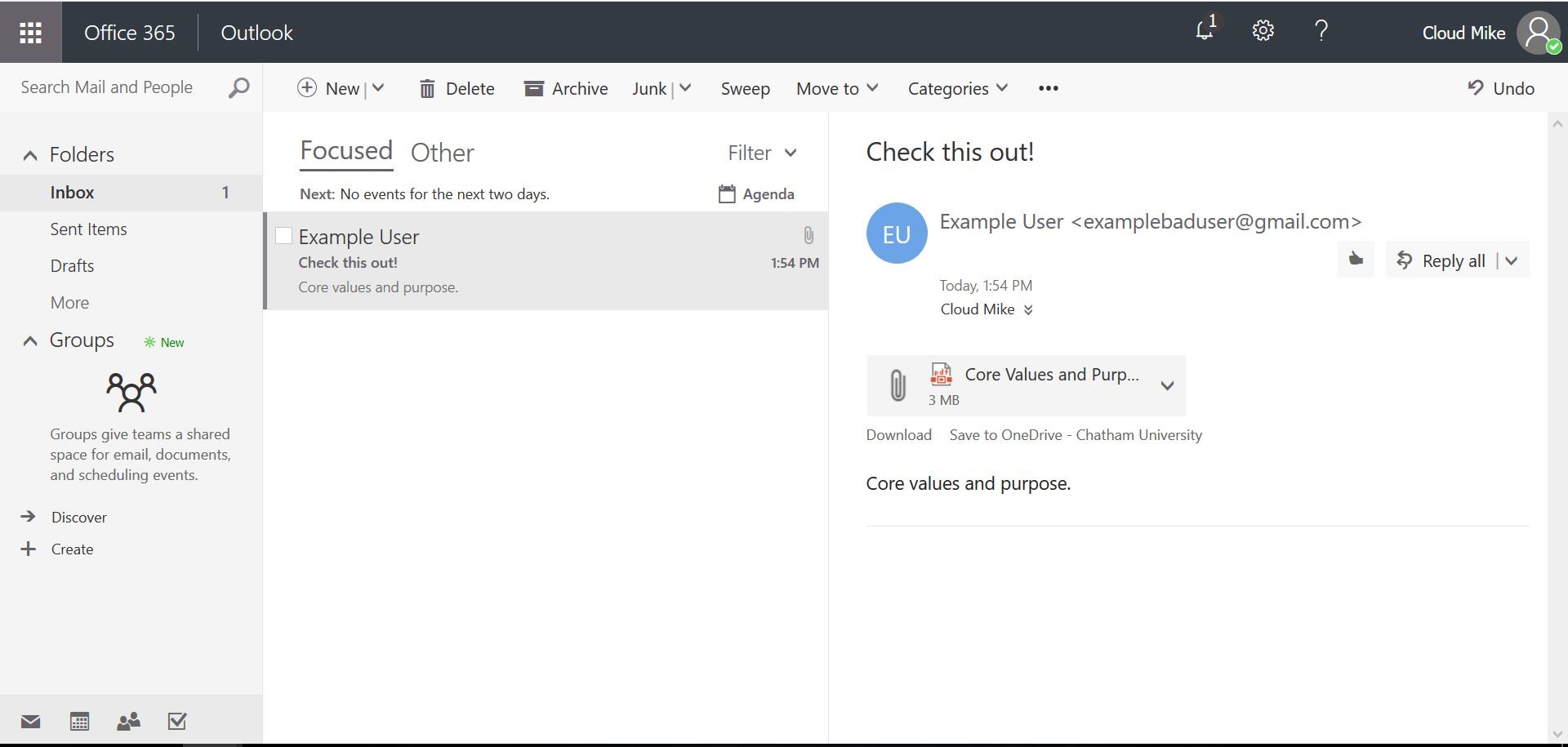
Clicking on the original attachment link labeled “Preview” will allow you to view the document in a safe manner until the full ATP scan is complete. In most cases, the scan will take only a few minutes to complete. Once complete, the attachment will reappear attached to the original email like you are accustomed to seeing.
We understand the temporary delay in opening attachments may seem like a slight nuisance, but the preview functionality should allow for the immediate review of most attachments while the system confirms the attachment does not contain malicious software. The few additional moments in time while a file is scanned is a small price to pay to ensure our organizations security.
Safe Links Feature
The safe links feature of ATP will protect Chatham from website links in emails that could potentially expose your computer to malicious software. The changes you will notice are minimal and the solution only becomes truly visible if a website link is malicious. The only changes you may notice is if you hover over the website link in the email. You will notice a URL to Microsoft like the following screenshot instead of to the website itself:
This Microsoft URL replacement is ATP protecting you by launching the website first on Microsoft’s systems to test the code coming from the website. If it is malicious, the website will be blocked and the malicious code will not make it to your computer. If the website passes the tests, you will be taken directly to the website. This entire process happens very quickly – little to no delay will be noticed.
As with all security related changes at Chatham, the goal is to improve overall usability of our systems while maintaining a secure computing environment for our users. If you have any follow up questions after reading this document, please contact Helpdesk.